The widespread adoption of blockchain technology has created multiple security risks that can affect users and the reputation of new projects. Blockchain technology has provided a new approach for conducting financial transactions and information exchange. However, the growing use of blockchain technology and the financial value associated with different blockchain and web3 projects has created multiple security concerns. The Sybil attack in blockchain is one of the top examples of security risks alongside flash loan attacks, phishing attacks, and rug pull scams.
It is important to learn about the impact and different types of Sybil attacks to find the best preventative measures. Let us learn more about the Sybil attack with examples and the trusted methods for preventing such security risks.
Definition of Sybil Attacks
The best way to understand Sybil attacks in blockchain would start with their definition. Sybil attacks use a single node for running different active fake identities concurrently on a decentralized or peer-to-peer network. Such types of attacks focus on undermining the authority in a reputable decentralized system by gaining control over a major share of nodes in the network.
The fake identities help in gaining a major share of influence over a network. Successful Sybil attacks involve threat actors who could carry out unauthorized actions within the system. For example, it could empower a single entity, such as a node, to create and operate multiple identities through IP-based accounts and user accounts.
The fake identities worsen the Sybil attacks impacts on blockchain by tricking the network and other users into believing that they are real. The interesting story behind the origin of the term ‘Sybil attacks’ comes from a 1973 book known as Sybil. In the book, one of the central characters, Sybil, suffers from dissociative identity disorder.
Build your identity as a certified blockchain expert with 101 Blockchains’ Blockchain Certifications designed to provide enhanced career prospects.
Types of Sybil Attacks
Most of the guides on how to prevent Sybil attack in blockchain undermine one of the most important aspects of the attacks. John R. Douceur explained the nature of Sybil attacks and the two variants of Sybil attacks in his research paper. The two types of Sybil attacks are the direct Sybil attack and indirect Sybil attack. Awareness of the implications of these two types of Sybil attacks can help in finding the ideal preventive measures for them.
Direct Sybil attack happens when a malicious node interacts directly with the honest nodes within the protocol. Such types of attacks are more effective as the authentic nodes cannot detect the fake nodes. On top of it, attackers could manipulate genuine nodes to take actions that could align with the self-interests of attackers.
Another important detail you must notice for Sybil attack prevention strategies is the effect of indirect Sybil attacks. Indirect Sybil attacks occur when the fake nodes interact with one or multiple nodes associated with the authentic nodes. As compared to a direct Sybil attack, hackers would utilize intermediary or proxy nodes for launching indirect attacks.
The intermediary nodes in between the authentic nodes and Sybil node would serve as representatives of a single point of failure. Hackers could exploit the intermediary nodes and launch an attack on honest nodes. The problem with indirect Sybil attacks is that they cannot be detected as easily as direct Sybil attacks. Once a Sybil node influences the middle nodes, it could lead to breaches in authentic nodes.
Get familiar with the terms related to blockchain with Blockchain Basics Flashcards.
What are the Causes of Sybil Attacks?
Sybil attacks have emerged as one of the critical security threats that have affected many blockchain networks. One of the foremost aspects of blockchain attacks and preventive measures is the identification of factors that trigger Sybil attacks. The first cause of Sybil attacks is the vulnerability in the node creation process. If the process for creating and running a node is easier, then any hacker could set up different Sybil nodes and implement the attack.
Another cause of Sybil attack in blockchain is the lack of an effective node validation system. With the right validation system, you can easily detect and resolve the problem of Sybil attacks. However, possibilities for manipulation of the validation system could trigger hackers to implement a Sybil attack.
The high volume of financial transactions on blockchain networks also serves as a trigger for Sybil attacks. Therefore, blockchain protocols with a high volume of financial transactions are likely to be vulnerable to Sybil attacks.
Start learning Blockchain with World’s first Blockchain Skill Paths with quality resources tailored by industry experts Now!
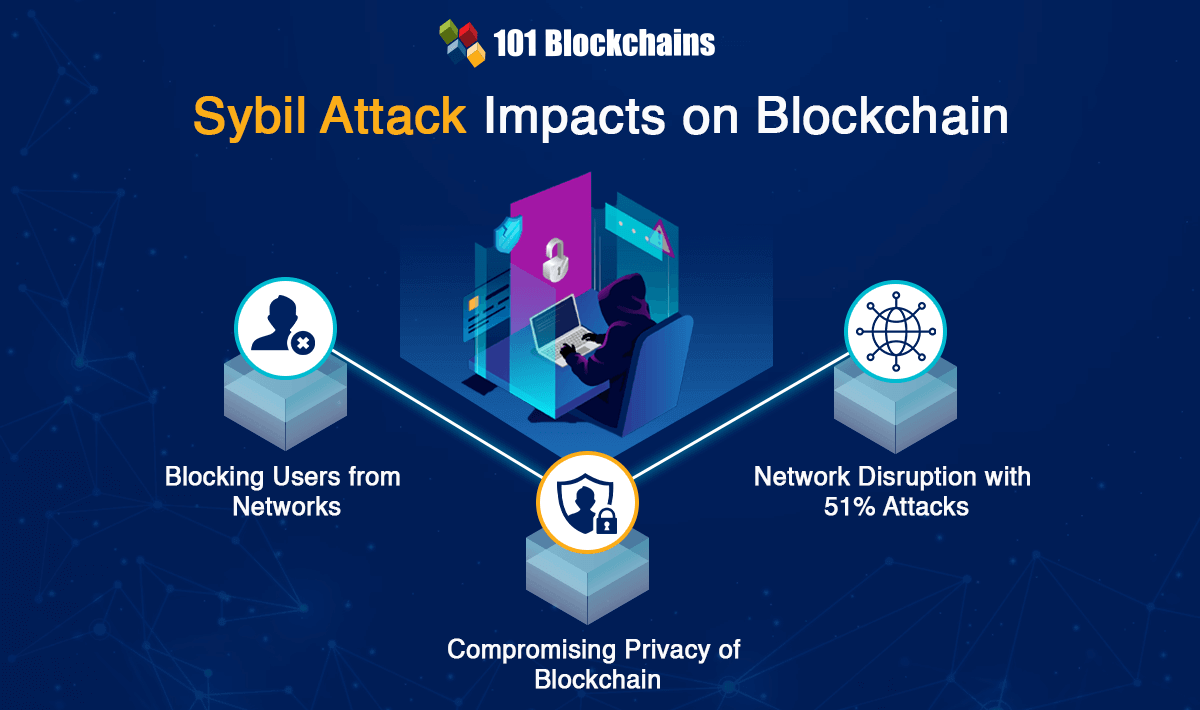
Impact of Sybil Attacks
The most crucial step in determining the ideal solution to Sybil attacks is detection. You must learn about best practices for Sybil attack detection to avoid their detrimental effect. If you have a few false identities on the blockchain network, then it may not present a problem. However, multiple fake identities could have a massive impact on the network. Here is an overview of the different ways in which Sybil attack can have a negative impact.
-
Blocking Users from Networks
The foremost highlight in the effects of Sybil attack on blockchain networks is the restriction of users from blockchain networks. Discussions on how to prevent Sybil attack in blockchain would draw attention to the problems with creation of fake identities. The fake nodes could overpower the authentic nodes in a blockchain network.
After Sybil nodes gain control of the network, they could completely change the ways in which the network operates. Most important of all, Sybil nodes could refuse the transmission or addition of blocks within a network. As a result, the fake node could block other users from accessing the network. The attacks could cause a temporary drop in crypto values that can damage the reputation of blockchain protocols.
-
Compromising Privacy of Blockchain
Nodes are the integral components in a blockchain network and manage the flow of information in the network. Therefore, any type of compromised node leads to privacy risks. The need for Sybil attack prevention strategies emerges from concerns regarding severity of privacy risks for blockchain networks. Sybil nodes can extract information about other nodes in the network.
On top of it, a Sybil attack could also lead to compromised IP addresses of users which can help in creating more fake nodes. Privacy breaches are more impactful for peer-to-peer networks. For example, hackers could use Sybil nodes to spy on data transfers and monitor network traffic.
-
Network Disruption with 51% Attacks
The most common purpose of a Sybil attack is to implement a 51% attack on blockchain networks. One of the easiest ways for Sybil attack detection focuses on checking for a 51% attack. Such types of attacks involve 51% of the network featuring false nodes. The fake Sybil nodes could overpower the votes of the other honest nodes in the network.
Such types of Sybil attacks can cause issues regarding votes on major operational decisions for the blockchain network. The 51% attack can help prevent confirmation of transactions or ordering new transactions in the interests of hackers. Hackers could also implement transaction reversal for double-spending.
Start your blockchain journey now with the Blockchains Fundamentals Course
Examples of Sybil Attacks
The impact of Sybil attacks shows that they can cause a lot of problems. Any blockchain network is susceptible to Sybil attacks. If you learn about different blockchain attacks and preventive measures, you will find that the examples of a blockchain attack in the real world could provide valuable information. One of the most prominent examples of a Sybil attack is the attack on Verge cryptocurrency protocol in 2021. Hackers implemented the Sybil attack to reorganize the blockchain network, in which they deleted transactions of more than 200 days.
Sybil attack has also been used to compromise the privacy of blockchain networks. Certain types of cryptocurrencies, such as Monero, focus on offering secure and private methods for completing transactions. The Sybil attacks blockchain examples point to the attack on Monero in 2020, in which a hacker disrupted the network and linked transactions to the IP addresses. Even if Monero managed to stop the attack, it could not prevent the leak of private user information.
Another prominent addition among the earliest examples of Sybil attack is the Tor attack in 2014. The example of the attack on Tor showcased the vulnerability of peer-to-peer networks to Sybil attacks. Attackers used the Sybil attack to discover the identities and locations of Tor users. One of the important highlights of the attack is that one hacker-controlled almost 115 different relays from one IP address. As a result, the hacker gained control over the network and accessed important private information.
Tor also provided another example of a Sybil attack in blockchain in 2020, as hackers compromised the network with a different motive. The attackers focused on Bitcoin owners who use Tor network. The hacker gained control over majority of fake Tor relays and intercepted Bitcoin transactions by users. Subsequently, the attacker used the information to strip Bitcoin owners of their funds.
What is the Ideal Solution for Preventing Sybil Attacks?
Bigger blockchain networks such as Bitcoin are difficult to exploit with a Sybil attack. However, you should know that Sybil attack prevention strategies are suitable for all types of blockchains. The impact of Sybil attacks might seem overwhelming and you might experience problems in dealing with the consequences, such as loss of private information or crypto assets. On the other hand, you can implement preventive measures to halt the assaults before they take place. Here are the most effective measures for preventing the attacks.
-
Developing a Reputation System
The most important highlight in Sybil blockchain attacks and preventive measures would point to the need for developing a reputation system. Sybil attacks rely on continuous growth in the number of fake identities. Therefore, a reputation system could help different members have unique levels of authority in the network.
Generally, members who have been a part of the system for a longer period have the capability to perform more interactions. However, you could not just implement such types of reputation systems without complications. It puts responsibility on the individual users in the network.
The reputation mechanism can validate older members as honest nodes and give them the power to override Sybil nodes. Reputation mechanisms can discourage attackers as they would move to an easier target without wasting time in creating new accounts and waiting for power over the network.
-
Identity Validation Mechanism
One of the most noticeable consequences of Sybil attacks is the risk of losing your privacy. If you have a problem with privacy, then a reputation mechanism is not the complete solution. The effective route for Sybil attack detection would draw attention towards validation of identity of new nodes. You can use identity validation mechanisms for direct validation in which a central authority would validate all the new nodes. Some systems could rely on indirect validation where verified nodes would vouch for the identity of new nodes.
Another trusted addition among measures for preventing Sybil attacks points at social trust graphs. Social trust graphs work through a comprehensive analysis of connectivity data between the nodes. Therefore, it can help in identifying and stopping abnormal nodes before they impose any damage.
The answers for ‘how to prevent Sybil attack in blockchain’ guide users towards different techniques for leveraging social trust graphs. For example, some users depend on sparsity-based metrics, and other mechanisms involve analysis of user attributes in a topological structure.
The graphs would then partition the part of the network with Sybil nodes and prevent them from manipulating the honest nodes. You can find different tools for using social trust graphs, such as SybilGuard, SybilRank, and SybilLimit. The best reason to use social trust graphs for preventing Sybil attacks is the ability to reduce the negative impact of the attack.
Start your journey to becoming an expert in Web3 security with the guidance of industry experts with Web3 Security Expert Career Path
Conclusion
The Sybil attack is one of the most threatening security risks in the domain of blockchain. As the threat of security risks jeopardizes blockchain adoption, it is important to focus on Sybil attack prevention strategies. The biggest problem with Sybil attack is that it involves the creation of fake nodes which appear as authentic nodes. It could not only affect the privacy of users but also lead to massive financial losses for users. Learn more about other security risks to blockchain and find the ideal ways for resolving the issues.

*Disclaimer: The article should not be taken as, and is not intended to provide any investment advice. Claims made in this article do not constitute investment advice and should not be taken as such. 101 Blockchains shall not be responsible for any loss sustained by any person who relies on this article. Do your own research!